PUA.Win64.ProcHack.AC
2021年1月27日
:
HEUR:RiskTool.Win32.ProcHack.gen (KASPERSKY)
平台:
Windows
总体风险等级:
潜在破坏:
潜在分布:
感染次数:
信息暴露:


恶意软件类型:
Potentially Unwanted Application
有破坏性?:
没有
加密?:

In the Wild:
是的
概要
它以其他恶意软件释放的文件或用户访问恶意网站时不知不觉下载的文件的形式到达系统。
技术详细信息
文件大小: 1,719,840 bytes
报告日期: EXE
初始樣本接收日期: 2021年1月5日
新病毒详细信息
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
其他详细信息
该程序执行以下操作:
- It accepts the following parameters:
- -settings {filename of settings file} -> allows the user to specify the location of Process Hacker's settings file
- -nosettings -> sets the settings to their defaults at startup, and no settings are saved
- -noplugins -> disables plugins, even if the "Enable plugins" option is set
- -newinstance -> starts a new instance of Process Hacker, even if the "Allow only one instance" option is set
- -v -> forces Process Hacker's main window to be displayed at startup, even if the "Start hidden" option is enabled.
- -hide -> hides Process Hacker's main window at startup, even if the "Start hidden" option is disabled
- -elevate -> prompts for elevation if Process Hacker is not started with elevated privileges.
- -c -ctype objecttype -cobject object -caction action -cvalue value -> enables command mode
- Possible values of objecttype:
- process
- service
- thread
- Possible values of object:
- process ID
- service name
- thread ID
- Possible values of action:
- For process:
- terminate
- suspend
- resume
- priority
- iopriority
- pagepriority
- For service:
- start
- continue
- pause
- stop
- delete
- For thread:
- terminate
- suspend
- resume
- For process:
- Possible values of objecttype:
- -s -> enables silent mode, no error messages are displayed for command mode, -installkph and -uninstallkph
- -ras -> enters run-as-service mode
- -nokph -> disables KProcessHacker, Process Hacker will not attempt to load the driver or connect to it
- -installkph -> installs KProcessHacker as a System Start service
- -uninstallkph -> deletes the KProcessHacker service
- -debug -> shows the debug console early in the startup process
- -showoptions -hwnd parentwindow -point x,y -> displays the Advanced tab of the options window only. parentwindow specifies the parent window handle in hexadecimal and x,y specifies the location of the options window.
- -phsvc -> enters phsvc mode which exposes a LPC-based API currently used by Process Hacker for tasks that require elevation.
- -priority r|h|n|l -> sets the priority of Process Hacker to realtime (r), high (h), normal (n) or idle (l).
- -selectpid pid -> selects pid in a new or existing instance of Process Hacker.
- -sysinfo section -> opens the System Information window at startup, and optionally navigates to the specified section.
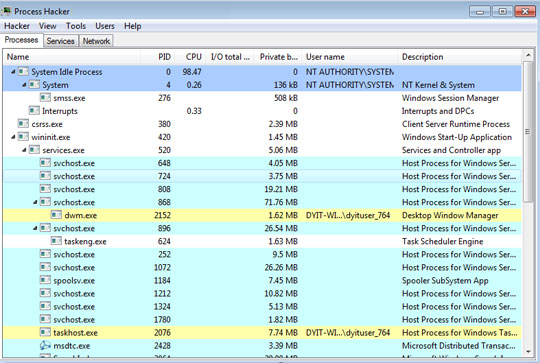
- It has the following display:
- Due to its side-loading vulnerability, this tool has been abused by other malware to kill security-related software by loading a stager DLL via DLL search order hijacking.
解决方案
最小扫描引擎: 9.800
SSAPI样式文件: 2.373.00
SSAPI样式发布日期: 2021年1月27日
Step 1
对于Windows ME和XP用户,在扫描前,请确认已禁用系统还原功能,才可全面扫描计算机。
Step 2
请注意,在执行此恶意软件/间谍软件/灰色软件期间,并非所有文件、文件夹、注册表项和条目都安装在您的计算机上。这可能是由于安装不完整或其他操作系统条件造成的。如果找不到相同的文件/文件夹/注册表信息,请继续下一步。
Step 3
使用趋势科技产品扫描计算机,并删除检测到的PUA.Win64.ProcHack.AC文件 如果检测到的文件已被趋势科技产品清除、删除或隔离,则无需采取进一步措施。可以选择直接删除隔离的文件。请参阅知识库页面了解详细信息。

