Ransom.MSIL.AGENDA.THJCOBD
Backdoor:MSIL/Androm.E!MTB (MICROSOFT)
Windows


恶意软件类型:
Ransomware
有破坏性?:
没有
加密?:
没有
In the Wild:
是的
概要
该勒索软件通过两种途径侵入系统:一是被其他恶意软件作为文件植入,二是用户访问恶意网站时在不知情的情况下下载的文件。
它会先执行,然后自行删除。
它会释放勒索说明文件作为赎金票据,并避免加密具有以下扩展名的文件:
技术详细信息
Arrival Details
该勒索软件通过两种途径侵入系统:一是被其他恶意软件作为文件植入,二是用户访问恶意网站时在不知情的情况下下载的文件。
Installation
该勒索软件会创建以下文件夹:
- %User Temp%\QLOG
(Note: %User Temp% 是当前用户的临时文件夹,通常位于此路径 C:\Documents and Settings\{user name}\Local Settings\Temp 在Windows 2000(32位)、XP及Server 2003(32位)系统上,或 C:\Users\{user name}\AppData\Local\Temp 在Windows Vista、7、8、8.1、2008(64位)、2012(64位)及10(64位)系统上。)
它会释放以下文件:
- %User Temp%\atx.bat → script to rename the first rh*.exe file it finds in the current folder to rh111.exe before executing it with specified arguments
- %User Temp%\QLOG\ThreadId({Number}).LOG → 内嵌配置与执行日志
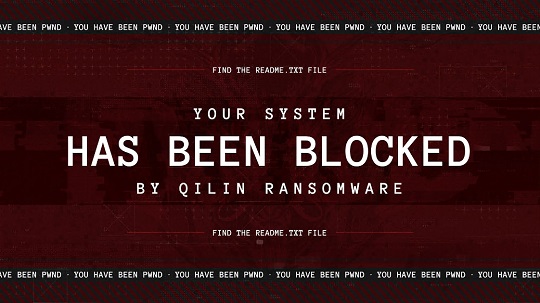
- %User Temp%\{Random Letters}.jpg → image used as desktop wallpaper
(Note: %User Temp% 是当前用户的临时文件夹,通常位于此路径 C:\Documents and Settings\{user name}\Local Settings\Temp 在Windows 2000(32位)、XP及Server 2003(32位)系统上,或 C:\Users\{user name}\AppData\Local\Temp 在Windows Vista、7、8、8.1、2008(64位)、2012(64位)及10(64位)系统上。)
它会添加以下进程:
- cmd /c ""%User Temp%\atx.bat" "
- "cmd" /C fsutil behavior set SymlinkEvaluation R2R:1
- "cmd" /C fsutil behavior set SymlinkEvaluation R2L:1
- "cmd" /C net use
- "cmd" /C wmic service where name='vss' call ChangeStartMode Manual
- "cmd" /C net start vss
- "cmd" /C vssadmin.exe delete shadows /all /quiet
- "cmd" /C net stop vss
- "cmd" /C wmic service where name='vss' call ChangeStartMode Disabled
- "powershell" $logs = Get-WinEvent -ListLog * | Where-Object {$_.RecordCount} | Select-Object -ExpandProperty LogName ; ForEach ( $l in $logs | Sort | Get-Unique ) {[System.Diagnostics.Eventing.Reader.EventLogSession]::GlobalSession.ClearLog($l)} - clears all event logs
- "powershell" -Command "Import-Module ActiveDirectory ; Get-ADComputer -Filter * | Select-Object -ExpandProperty DNSHostName"
- "powershell" -Command "ServerManagerCmd.exe -i RSAT-AD-PowerShell ; Install-WindowsFeature RSAT-AD-PowerShell ; Add-WindowsCapability -Online -Name 'RSAT.ActiveDirectory.DS-LDS.Tools~~~~0.0.1.0'"
- "reg.exe" QUERY "HKEY_USERS"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\.DEFAULT\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\{LOCAL SERVICE SID}\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\{NETWORK SERVICE SID}\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\{USER SID}\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\{USER CLSID}\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command "Set-ItemProperty -Path 'Registry::HKEY_USERS\{SYSTEM SID}\Control Panel\Desktop' -Name Wallpaper -Value '%User Temp%\{Random Letters}.jpg'"
- "powershell" -Command " REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImagePath /t REG_SZ /d '%User Temp%\{Random Letters}.jpg' /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImageUrl /t REG_SZ /d '%User Temp%\{Random Letters}.jpg' /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImageStatus /t REG_DWORD /d 1 /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImagePath /t REG_SZ /d '%User Temp%\{Random Letters}.jpg' /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImageUrl /t REG_SZ /d '%User Temp%\{Random Letters}.jpg' /f ; REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImageStatus /t REG_DWORD /d 1 /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImagePath /t REG_SZ /d %User Temp%\{Random Letters}.jpg /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImageUrl /t REG_SZ /d %User Temp%\{Random Letters}.jpg /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization /v LockScreenImageStatus /t REG_DWORD /d 1 /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImagePath /t REG_SZ /d %User Temp%\{Random Letters}.jpg /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImageUrl /t REG_SZ /d %User Temp%\{Random Letters}.jpg /f
- "%System%\reg.exe" ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP /v LockScreenImageStatus /t REG_DWORD /d 1 /f
- "cmd" /C timeout /T 10 & Del "{Malware Path}\{Malware Filename}"
(Note: %User Temp% 是当前用户的临时文件夹,通常位于此路径 C:\Documents and Settings\{user name}\Local Settings\Temp 在Windows 2000(32位)、XP及Server 2003(32位)系统上,或 C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %System% 是Windows系统文件夹,通常位于此路径 C:\Windows\System32 适用于所有Windows操作系统版本。)
它会先执行,然后自行删除。
它会添加以下互斥量,以确保在任何时候只有一个副本在运行:
- 32bcf09497d3a5a77fcea9740d3bd2b2c70760cfe3aef8b4c819adb509434ead
Autostart Technique
该勒索软件会添加以下注册表项,以实现每次系统启动时自动执行:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
*{Random Letters} = "{Malware Path}\{Malware Filename}" --password {Password} --no-admin
其他系统修改
This Ransomware modifies the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Control\FileSystem
SymlinkRemoteToLocalEvaluation = 1
注:该注册表项的默认值为 0.)
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Control\FileSystem
SymlinkRemoteToRemoteEvaluation = 1
注:该注册表项的默认值为 0.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
EnableLinkedConnections = 1
注:该注册表项的默认值为 0.)
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\LanmanServer\Parameters
MaxMpxCt = 65535
注:该注册表项的默认值为 {Default Value}.)
它通过修改以下注册表项来更改桌面壁纸:
HKEY_CURRENT_USERS\Control Panel\Desktop
Wallpaper = %User Temp%\{Random Letters}.jpg
注:该注册表项的默认值为 {Default Image}.)
HKEY_USERS\.DEFAULT\Control Panel\
Desktop
Wallpaper = %User Temp%\{Random Letters}.jpg
注:该注册表项的默认值为 {Default Image}.)
HKEY_USERS\{LOCAL SERVICE SID}\Control Panel\
Desktop
Wallpaper = %User Temp%\{Random Letters}.jpg
注:该注册表项的默认值为 {Default Image}.)
HKEY_USERS\{NETWORK SERVICE SID}\Control Panel\
Desktop
Wallpaper = %User Temp%\{Random Letters}.jpg
注:该注册表项的默认值为 {Default Image}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Personalization
LockScreenImagePath = %User Temp%\{Random Letters}.jpg
注:该注册表项的默认值为 {Default Image Path}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Personalization
LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
注:该注册表项的默认值为 {Default Image URL}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Personalization
LockScreenImageStatus = 1
注:该注册表项的默认值为 {Default Value}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\PersonalizationCSP
LockScreenImagePath = %User Temp%\{Random Letters}.jpg
注:该注册表项的默认值为 {Default Image Path}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\PersonalizationCSP
LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
注:该注册表项的默认值为 {Default Image URL}.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\PersonalizationCSP
LockScreenImageStatus = 1
注:该注册表项的默认值为 {Default Value}.)
它将系统桌面壁纸设置为以下图像:
进程终止
若在受感染系统上发现以下服务,该勒索软件会将其终止:
- (.*?)sql(.*?)
- acronisagent
- acrsch2svc
- backup
- backupexecagentaccelerator
- backupexecagentbrowser
- backupexecdivecimediaservice
- backupexecjobengine
- backupexecmanagementservice
- backupexecrpcservice
- backupexecvssprovider
- gxblr
- gxcimgr
- gxclmgrs
- gxcvd
- gxfwd
- gxmmm
- gxvss
- gxvsshwprov
- memtas
- mepocs
- msexchange
- msexchange\$
- mvarmor
- mvarmor64
- pdvfsservice
- qbcfmonitorservice
- qbdbmgrn
- qbidpservice
- sap
- sap\$
- sapd\$
- saphostcontrol
- saphostexec
- sapservice
- sophos
- sql
- veeam
- veeamdeploymentservice
- veeamnfssvc
- veeamtransportsvc
- vsnapvss
- vss
- wsbexchange
若在受感染系统的内存中发现以下进程正在运行,该勒索软件会将其终止:
- agntsvc
- avagent
- avscc
- bedbh
- benetns
- bengien
- beserver
- cagservice
- cvd
- cvfwd
- cvmountd
- cvods
- dbeng50
- dbsnmp
- dellsystemdetect
- encsvc
- enterpriseclient
- excel
- firefox
- infopath
- isqlplussvc
- msaccess
- mspub
- mvdesktopservice
- mydesktopqos
- mydesktopservice
- notepad
- ocautoupds
- ocomm
- ocssd
- onenote
- oracle
- outlook
- powerpnt
- pvlsvr
- qbcfmonitorservice
- qbdbmgrn
- qbidpservice
- raw_agent_svc
- sap
- saphostexec
- saposcol
- sapstartsrv
- sqbcoreservice
- sql
- steam
- synctime
- tbirdconfig
- teamviewer
- teamviewer_service
- thebat
- thunderbird
- tv_w32
- tv_x64
- veeamdeploymentsvc
- veeamnfssvc
- veeamtransportsvc
- visio
- vmcompute
- vmwp
- vsnapvss
- vxmon
- winword
- wordpad
- xfssvccon
其他信息
该勒索软件会执行以下操作:
- It enables the following privileges to allow access to restricted actions in the system:
- SeDebugPrivilege
- SeImpersonatePrivilege
- SeIncreaseBasePriorityPrivilege
- It creates the following named pipe:
- \.\pipe\__rust_anonymous_pipe1__.3860.{Number Count}
- It repeatedly clears all event logs in the system.
- It retrieves the DNS hostnames of all computers in an Active Directory domain before encrypting them.
- It deletes all shadow copies and disables automatic startup of Volume Shadow Copy Service
它接受以下参数:
- --debug → enables debugging mode
- --dry-run → tests file encryption then restores files back to original
- --escalated → run with elevated privileges
- --exclude {Host to Exclude} → excludes specified hosts when self-propagating
- --fde
- --force
- --impersonate {Account} → uses the specified account for impersonation
- --ips {IP Addresses} → encrypts hosts with specified IP addresses
- --kill-cluster → disables VM clusters
- --logs → compresses the logs into a ZIP file and saves as {Malware Path}\QLOGS.zip
- --no-admin → disables running as admin
- --no-autostart → disables creating autostart
- --no-delete → disables deleting folders
- --no-destruct → disables self-destruct
- --no-df → disables using the directory name filter
- --no-domain → disables encrypting files on domain hosts
- --no-ef → disables using the file extension filter
- --no-escalate → disables privilege escalation
- --no-extension → disables appending extension to the encrypted files
- --no-ff → disables using a filename filter
- --no-local → disables encrypting files on the local system
- --no-logs → disables logging
- --no-mounted → disables mounting drives for encryption
- --no-network → disables encrypting files on network shares
- --no-note → disables dropping ransom note
- --no-priority → disables prioritization during encryption
- --no-proc → disables process termination
- --no-sandbox → disables the detection of running in a virtual machine
- --no-services → disables stopping system services
- --no-vm → disables stopping virtual machines
- --no-wallpaper → disables setting the desktop wallpaper
- --no-zero → disables free space cleanup of host disks
- --parent-sid {SID} → passes the SID of the user of the parent process to the program
- --password {Password} → specifies a password to run the ransomware
- --paths {Directories} → encrypts files at specified paths
- --print-delay {Seconds} → delay before printing
- --print-image → enables printing the image
- --safe → reboots into safe mode before encrypting files
- --spread → enables self-propagation
- --spread-process → indicates the program that it is running in self-propagation
- --spread-vcenter → self-propagate using vCenter
- --timer {Seconds} → sets the waiting time in seconds before encryption and other actions are performed
Ransomware Routine
该勒索软件会避免加密文件名中包含以下字符串的文件:
- #recycle
- autorun.inf
- autorun.ini
- boot.ini
- bootfont.bin
- bootmgfw.efi
- bootmgr
- bootmgr.efi
- bootsect.bak
- desktop.ini
- iconcache.db
- ntldr
- ntuser.dat
- ntuser.dat.log
- ntuser.ini
- thumbs.db
它会避免加密以下文件夹中的文件:
- .
- ..
- $recycle.bin
- $windows.~bt
- $windows.~ws
- admin$
- appdata
- application data
- boot
- config.msi
- intel
- ipc$
- mozilla
- msocache
- netlogon
- perflogs
- program files
- program files (x86)
- programdata
- system volume information
- sysvol
- tor browser
- windows
- windows.old
它会为加密文件的文件名添加以下扩展名:
- .FFzjdLtZ4C
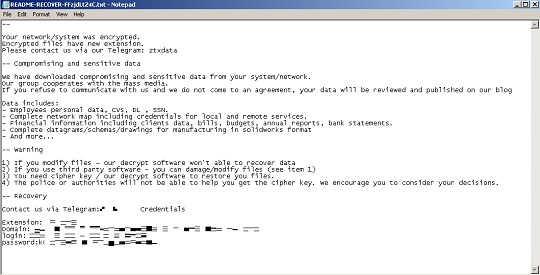
它会释放以下文件作为勒索信:
- {Encrypted Path}\README-RECOVER-FFzjdLtZ4C.txt
它会避免加密具有以下文件扩展名的文件:
- .386
- .adv
- .ani
- .bat
- .bin
- .cmd
- .com
- .cpl
- .cur
- .deskthemepack
- .diagcab
- .diagcfg
- .diapkg
- .dll
- .drv
- .exe
- .hlp
- .hta
- .icl
- .icns
- .ico
- .ics
- .idx
- .key
- .lnk
- .lock
- .mod
- .mpa
- .msc
- .msi
- .msp
- .msstyles
- .msu
- .nls
- .nomedia
- .ocx
- .pdb
- .prf
- .ps1
- .rom
- .rtp
- .scr
- .shs
- .spl
- .sys
- .theme
- .themepack
- .wpx
- .FFzjdLtZ4C
解决方案
Step 1
亚信安全测性机器学习可在恶意软件初现时、尚未在系统执行前便及时检测并拦截。启用此功能后,您的亚信安全产品会使用以下机器学习命名标识检测该恶意软件:
- TROJ.Win32.TRX.XXPE50FFF086
Step 2
在进行任何扫描之前,Windows 7、Windows 8、Windows 8.1 和 Windows 10 用户必须先执行以下操作: 禁用 系统还原 以便对电脑进行全面扫描。
Step 3
注意:在此恶意软件/间谍软件/灰色软件执行期间,并非所有文件、文件夹和注册表键值和项都会安装到您的计算机上。这可能是由于不完整的安装或其他操作系统条件所致。如果您没有找到相同的文件/文件夹/注册表信息,请继续进行下一步操作。
Step 4
以安全模式重启
要进入安全模式重启:
• For Windows 7 and Windows Server 2008 (R2) users
- 重启你的电脑。
- 按下F8 在开机自检(POST)程序完成后。如果 高级启动选项 若未出现菜单,请尝试重启计算机,并在POST界面显示后多次按F8键。
- 在高级启动选项菜单中,使用方向键选择Safe Mode 选项,然后按 Enter.
• For Windows 8, Windows 8.1, and Windows Server 2012 users
- 访问Charms bar 将鼠标指针移至屏幕右上角即可。
- 将鼠标指针向下移动并点击 Settings>更改您的电脑设置.
- 在左侧面板中,点击“通用”。
- 在右侧面板中,向下滚动至底部找到 Advanced startup 部分,然后点击 Restart now 按钮并等待系统重启。
- 在Advanced Startup 菜单中,点击 Troubleshoot>Advanced Options>Startup Settings>Restart 并等待系统重启。
- 在Startup Settings 菜单中,按下 4 以启用安全模式。
• 对于 Windows 10 用户:
- 按下Windows logo key + I 键打开“设置”。若无效,请选择 Start按钮,然后选择Settings.
- 选择Update & Security > Recovery.
- 在Advanced startup, select Restart now.
- 当您的电脑重启进入 请选择一个选项 屏幕上,选择Troubleshoot > Advcanced options > 启动设置 > Restart.
- 电脑重启后,您将看到一系列选项。请选择4 或按 F4 以安全模式启动您的电脑。
Step 5
删除此注册表值
Important: 编辑 Windows Registry 操作不当可能导致系统出现无法恢复的故障。请务必仅在您熟悉相关步骤的情况下执行;如有疑问,可寻求系统管理员的协助。否则,请查看下方链接。 Microsoft article 修改计算机注册表前请务必先进行此操作.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- *{Random Letters} = "{Malware Path}\{Malware Filename}" --password {Password} --no-admin
- *{Random Letters} = "{Malware Path}\{Malware Filename}" --password {Password} --no-admin
要删除此恶意软件创建的注册表值:
- 打开注册表编辑器。 为此,请执行以下操作:
» 对于 Windows 7 和 Windows Server 2008 (R2) 用户,请点击 Start button, type regedit in the Search输入字段,然后按下Enter.
» 对于 Windows 8、Windows 8.1、10 及 Windows Server 2012 (R2) 用户,请右键单击屏幕左下角,点击 Run, type regedit 在提供的文本框中,然后点击 Enter. - 在注册表编辑器窗口的左侧面板中,双击以下项目:
HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Windows>CurrentVersion>Run - 在右侧面板中,找到并删除以下条目:
*{Random Letters} = "{Malware Path}\{Malware Filename}" --password {Password} --no-admin - 关闭注册表编辑器。
Step 6
还原已修改注册表值。
Important: 编辑 Windows Registry 操作不当可能导致系统出现无法恢复的故障。请务必仅在您熟悉相关步骤的情况下执行;如有疑问,可寻求系统管理员的协助。否则,请查看下方链接。 Microsoft article 修改计算机注册表前请务必先进行此操作.
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\FileSystem
- SymlinkRemoteToLocalEvaluation = 1
- SymlinkRemoteToLocalEvaluation = 1
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\FileSystem
- SymlinkRemoteToRemoteEvaluation = 1
- SymlinkRemoteToRemoteEvaluation = 1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- EnableLinkedConnections = 1
- EnableLinkedConnections = 1
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\LanmanServer\Parameters
- MaxMpxCt = 65535
- MaxMpxCt = 65535
- In HKEY_CURRENT_USERS\Control Panel\Desktop
- Wallpaper = %User Temp%\{Random Letters}.jpg
- Wallpaper = %User Temp%\{Random Letters}.jpg
- In HKEY_USERS\.DEFAULT\Control Panel\Desktop
- Wallpaper = %User Temp%\{Random Letters}.jpg
- Wallpaper = %User Temp%\{Random Letters}.jpg
- In HKEY_USERS\{LOCAL SERVICE SID}\Control Panel\Desktop
- Wallpaper = %User Temp%\{Random Letters}.jpg
- Wallpaper = %User Temp%\{Random Letters}.jpg
- In HKEY_USERS\{NETWORK SERVICE SID}\Control Panel\Desktop
- Wallpaper = %User Temp%\{Random Letters}.jpg
- Wallpaper = %User Temp%\{Random Letters}.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization
- LockScreenImagePath = %User Temp%\{Random Letters}.jpg
- LockScreenImagePath = %User Temp%\{Random Letters}.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization
- LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
- LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization
- LockScreenImageStatus = 1
- LockScreenImageStatus = 1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP
- LockScreenImagePath = %User Temp%\{Random Letters}.jpg
- LockScreenImagePath = %User Temp%\{Random Letters}.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP
- LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
- LockScreenImageUrl = %User Temp%\{Random Letters}.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP
- LockScreenImageStatus = 1
- LockScreenImageStatus = 1
要恢复被该恶意/灰色软件修改的注册表值,请执行以下操作:
- 打开注册表编辑器。
» 对于 Windows 7 和 Server 2008 (R2) 用户,请点击 Start button, type regedit in the Search输入字段,然后按下Enter.
» 对于 Windows 8、8.1、10 及 Server 2012 (R2) 用户,请右键单击屏幕左下角,点击 Run, type regedit 在提供的文本框中,然后点击 Enter. - 在左侧面板中,双击以下项目:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\FileSystem - 在右侧面板中,找到注册表值:
SymlinkRemoteToLocalEvaluation = 1 - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
SymlinkRemoteToLocalEvaluation = 0 - Again 在右侧面板中,找到注册表值:
SymlinkRemoteToRemoteEvaluation = 1 - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
SymlinkRemoteToRemoteEvaluation = 0 - 在左侧面板中,双击以下项目:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System - 在右侧面板中,找到注册表值:
EnableLinkedConnections = 1 - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
EnableLinkedConnections = 0 - 在左侧面板中,双击以下项目:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\LanmanServer\Parameters - 在右侧面板中,找到注册表值:
MaxMpxCt = 65535 - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
MaxMpxCt = {Default Value} - 在左侧面板中,双击以下项目:
HKEY_CURRENT_USERS\Control Panel\Desktop - 在右侧面板中,找到注册表值:
Wallpaper = %User Temp%\{Random Letters}.jpg - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
Wallpaper = {Default Image} - 在左侧面板中,双击以下项目:
HKEY_USERS\.DEFAULT\Control Panel\Desktop - 在右侧面板中,找到注册表值:
Wallpaper = %User Temp%\{Random Letters}.jpg - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
Wallpaper = {Default Image} - 在左侧面板中,双击以下项目:
HKEY_USERS\{LOCAL SERVICE SID}\Control Panel\Desktop - 在右侧面板中,找到注册表值:
Wallpaper = %User Temp%\{Random Letters}.jpg - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
Wallpaper = {Default Image} - 在左侧面板中,双击以下项目:
HKEY_USERS\{NETWORK SERVICE SID}\Control Panel\Desktop - 在右侧面板中,找到注册表值:
Wallpaper = %User Temp%\{Random Letters}.jpg - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
Wallpaper = {Default Image} - 在左侧面板中,双击以下项目:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Personalization - 在右侧面板中,找到注册表值:
LockScreenImagePath = %User Temp%\{Random Letters}.jpg - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
LockScreenImagePath = {Default Image Path} - Again 在右侧面板中,找到注册表值:
LockScreenImageUrl = %User Temp%\{Random Letters}.jpg - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
LockScreenImageUrl = {Default Image URL} - Again 在右侧面板中,找到注册表值:
LockScreenImageStatus = 1 - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
LockScreenImageStatus = {Default Value} - 在左侧面板中,双击以下项目:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\PersonalizationCSP - 在右侧面板中,找到注册表值:
LockScreenImagePath = %User Temp%\{Random Letters}.jpg - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
LockScreenImagePath = {Default Image Path} - Again 在右侧面板中,找到注册表值:
LockScreenImageUrl = %User Temp%\{Random Letters}.jpg - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
LockScreenImageUrl = {Default Image URL} - Again 在右侧面板中,找到注册表值:
LockScreenImageStatus = 1 - Right-click on the value name 并选择“修改”。更改 value data of this entry to:
LockScreenImageStatus = {Default Value} - 关闭注册表编辑器。
Step 7
搜索并删除这些文件
- %User Temp%\atx.bat
- %User Temp%\QLOG\ThreadId({Number}).LOG
- %User Temp%\{Random Letters}.jpg
- {Encrypted Path}\README-RECOVER-FFzjdLtZ4C.txt
要删除恶意软件/灰色软件文件:
适用于 Windows 7、Server 2008 (R2)、8、8.1、10 及 Server 2012 (R2) 系统:
- 打开 Windows 资源管理器窗口。
- 对于 Windows 7 和 Server 2008 (R2) 用户:点击Start>Computer.
- 对于Windows 8、8.1、10及Server 2012用户, 右键单击屏幕左下角,然后点击 File Explorer.
- 在搜索计算机/此电脑输入框中,键入:
- %User Temp%\atx.bat
- %User Temp%\QLOG\ThreadId({Number}).LOG
- %User Temp%\{Random Letters}.jpg
- {Encrypted Path}\README-RECOVER-FFzjdLtZ4C.txt
- 定位到该文件后,选中并按 SHIFT+DELETE 将其删除。
- 对所有列出的文件重复上述步骤。
*Note:阅读以下微软官方页面 若上述步骤在 Windows 7 和 Server 2008 (R2) 系统上无效:
Step 8
搜索并删除此文件夹
- %User Temp%\QLOG
要删除恶意软件/灰色软件文件夹:
- 右键单击“开始”按钮,然后点击 Search... or Find..., 根据您运行的 Windows 版本选择相应操作。
- 在“名称”输入框中键入:
- %User Temp%\QLOG
- 在Look In 下拉列表,选择 My Computer,然后按Enter键。
- 定位到该文件夹后,选中并按 Shift+Delete 组合键将其永久删除。
Step 9
以正常模式重启计算机,并使用亚信安全产品扫描检测病毒Ransom.MSIL.AGENDA.THJCOBD. 如果检测到的文件已被亚信安全产品清理、删除或隔离,则无需执行其他操作。您可以选择直接删除隔离文件。请勾选此项知识库页面 了解更多信息。
Step 10
从备份中还原加密文件。
Step 11
重置您的桌面属性
要恢复您的桌面壁纸:
- Click Start>Settings>Control Panel.
- Double-click the Display option and点击the Background tab.
- 点击Browse 按钮选择您喜欢的壁纸,或从 Windows built-in wallpapers.
- Choose OK以应用更改。
Step 12
使用您的亚信安全产品扫描电脑,删除被检测为以下名称的文件 Ransom.MSIL.AGENDA.THJCOBD. 若亚信安全产品已将检测到的文件清除、删除或隔离,则无需再执行任何额外步骤;您也可选择直接删除隔离区中的文件。更多信息请访问以下亚信安全支持页面: