Ransom.MSIL.EGOGEN.THEBBBC
Trojan:MSIL/XWormRAT.A!MTB (MICROSOFT)
Windows


恶意软件类型:
Ransomware
有破坏性?:
没有
加密?:
没有
In the Wild:
是的
概要
它以文件的形式出现在系统中,可能是其他恶意软件投放的,或者是用户在访问恶意网站时无意中下载的。
它添加某些注册表项,禁用任务管理器。该操作阻止用户通过任务管理器终止恶意软件进程。
如果检测到自身在虚拟环境中运行,它将终止运行。
技术详细信息
新病毒详细信息
它以文件的形式出现在系统中,可能是其他恶意软件投放的,或者是用户在访问恶意网站时无意中下载的。
安装
它植入下列文件:
- %AppDataLocal%\discord.exe
- %Application Data%\ID
- %Application Data%\fondo_antiguo.jpg → Copy of current background
- %User Profile%\Pictures\image[Random 30 characters].jpg → deleted afterwards
- %User Startup%\BXIuSsB.exe
- %User Temp%\Adobe\BXIuSsB.exe
- %User Temp%\[Random 7 characters]_dat.log
- %Application Data%\delback.bat
- %User Startup%\update.bat
(注意: %Application Data% 是当前用户的 Application Data 文件夹,通常位于 C:\Windows\Profiles\{user name}\Application Data (Windows 98 和 ME)、C:\WINNT\Profiles\{user name}\Application Data (Windows NT)、C:\Documents and Settings\{user name}\Local Settings\Application Data (Windows 2000(32-bit)、XP 和 Server 2003(32-bit)) 和 C:\Users\{user name}\AppData\Roaming (Windows Vista、7、8、8.1、2008(64-bit)、2012(64-bit) 和 10(64-bit))。. %User Profile% 是当前用户的概要文件文件夹,通常位于 C:\Windows\Profiles\{user name} (Windows 98 和 ME)、C:\WINNT\Profiles\{user name} (Windows NT)、C:\Documents and Settings\{user name} (Windows 2000(32-bit)、XP 和 Server 2003(32-bit)) 和 C:\Users\{user name} (Windows Vista、7、8、8.1、2008(64-bit)、2012(64-bit) 和 10(64-bit))。. %User Startup% 是当前用户的启动文件夹,通常位于 C:\Windows\Profiles\{user name}\Start Menu\Programs\Startup (Windows 98 和 ME)、C:\WINNT\Profiles\{user name}\Start Menu\Programs\Startup (Windows NT)、C:\Documents and Settings\{User name}\Start Menu\Programs\Startup (Windows 2003(32-bit)、XP、2000(32-bit)) 和 C:\Users\{user name}\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup (Windows Vista、7、8、8.1、2008(64-bit)、2012(64-bit)、10(64-bit))。. %User Temp% 是当前用户的 Temp 文件夹。通常位于 C:\Documents and Settings\{user name}\Local Settings\Temp (Windows 2000(32-bit)、XP 和 Server 2003(32-bit))、C:\Users\{user name}\AppData\Local\Temp (Windows Vista、7、8、8.1、2008(64-bit)、2012(64-bit) 和 10(64-bit)。)
它植入和执行下列文件:
- %User Startup%\1.exe
- %User Startup%\archive.exe
- %User Startup%\Xarch.exe
- %User Startup%\teleratserver.exe
(注意: %User Startup% 是当前用户的启动文件夹,通常位于 C:\Windows\Profiles\{user name}\Start Menu\Programs\Startup (Windows 98 和 ME)、C:\WINNT\Profiles\{user name}\Start Menu\Programs\Startup (Windows NT)、C:\Documents and Settings\{User name}\Start Menu\Programs\Startup (Windows 2003(32-bit)、XP、2000(32-bit)) 和 C:\Users\{user name}\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup (Windows Vista、7、8、8.1、2008(64-bit)、2012(64-bit)、10(64-bit))。)
它添加下列进程:
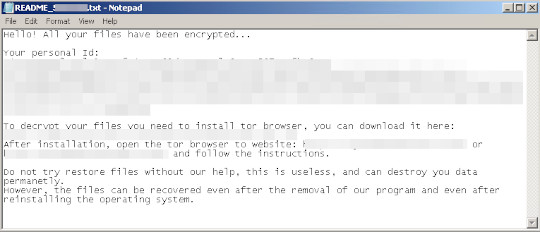
- %Application Data%\Read Me First!.txt
- cmd "/c @echo off & echo github: https://{BLOCKED}t.me/{BLOCKED}69 & start https://{BLOCKED}t.me/{BLOCKED}69"
- vssadmin delete shadows /all /quiet
- bcdedit.exe /set {default} recoveryenabled no
- bcdedit.exe /set {default} bootstatuspolicy ignoreallfailures
- ping -n 1 -w 5000 {BLOCKED}.{BLOCKED}.254.254
- del "%User Startup%\BXIuSsB.exe"
它创建下列文件夹:
- %User Temp%\Adobe → deleted after encryption
(注意: %User Temp% 是当前用户的 Temp 文件夹。通常位于 C:\Documents and Settings\{user name}\Local Settings\Temp (Windows 2000(32-bit)、XP 和 Server 2003(32-bit))、C:\Users\{user name}\AppData\Local\Temp (Windows Vista、7、8、8.1、2008(64-bit)、2012(64-bit) 和 10(64-bit)。)
自启动技术
它添加下列注册表项,在系统每次启动时自行执行:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
1 = %User Startup%\1.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
archive = %User Startup%\archive.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
Xarch = %User Startup%\Xarch.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
discord = %AppDataLocal%\discord.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
teleratserver = %User Startup%\teleratserver.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
BXIuSsB = %User Startup%\BXIuSsB.exe
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\RunOnce
BXIuSsB.exe = %User Temp%\Adobe\BXIuSsB.exe
其他系统修改
它添加下列注册表项,禁用任务管理器:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableTaskMgr = 1
它通过修改下列注册表项,更改桌面壁纸:
HKEY_CURRENT_USER\Control Panel\Desktop
Wallpaper = %User Profile%\Pictures\image[Random 30 characters].jpg
它将系统的桌面壁纸设置为下列图像:
进程终止
它终止在受感染的系统内存中运行的下列进程:
- taskmgr
- sqlagent
- winword
- sqlbrowser
- sqlservr
- sqlwriter
- oracle
- ocssd
- dbsnmp
- synctime
- mydesktopqos
- agntsvc.exeisqlplussvc
- xfssvccon
- mydesktopservice
- ocautoupds
- agntsvc.exeagntsvc
- agntsvc.exeencsvc
- firefoxconfig
- tbirdconfig
- ocomm
- mysqld
- sql
- mysqld-nt
- mysqld-opt
- dbeng50
- sqbcoreservice
其他详细信息
如果检测到自身在虚拟环境中运行,它将终止运行。
该程序执行以下操作:
- It does not proceed with its encryption routine if one of the following conditions are met:
- Registry data under HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\Disk\Enum contains the following strings:
- VBOX
- Virtual
- VMware
- Processes contain the following strings:
- VBox
- prl_
- srvc.exe
- vmtoolsd
- Registry data under HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\Disk\Enum contains the following strings:
- It will drop this ransom note instead if it meets one of the following conditions:
- If the OS name contains "Serv" and System Language is one of the following:
- Arabic, Dutch, English, French, German, Italian, Korean, Portuguese, Spanish, Swedish, Bulgarian, Catalan, Czech, Danish, Greek, Estonian, Basque, Finnish, Hungarian, Japanese, Lithuanian, Norwegian, Polish, Romanian, Sami, Slovak, Slovenian, Turkish
- The number of encrypted files is greater than 5000
- Renames the encrypted files to [(Original File Name) converted to base64]
- It encrypts fixed, removable and network drives
- It terminates if the machine has the following system language:
- Russian
- Belarusian
- Ukrainian
- Kazakh
- Armenian
- Georgian
- Tatar
- Uzbek
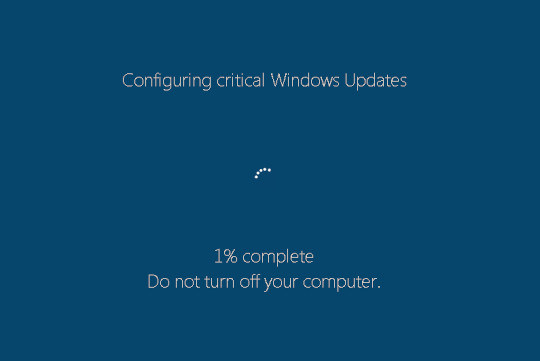
- Displays a fake Windows Update upon installation
解决方案
Step 2
对于Windows ME和XP用户,在扫描前,请确认已禁用系统还原功能,才可全面扫描计算机。
Step 3
注意:在此恶意软件/间谍软件/灰色软件执行期间,并非所有文件、文件夹和注册表键值和项都会安装到您的计算机上。这可能是由于不完整的安装或其他操作系统条件所致。如果您没有找到相同的文件/文件夹/注册表信息,请继续进行下一步操作。
Step 4
删除该注册表值
注意事项:错误编辑Windows注册表会导致不可挽回的系统故障。只有在您掌握后或在系统管理员的帮助下才能完成这步。或者,请先阅读Microsoft文章,然后再修改计算机注册表。
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- 1 = %User Startup%\1.exe
- 1 = %User Startup%\1.exe
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- archive = %User Startup%\archive.exe
- archive = %User Startup%\archive.exe
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- Xarch = %User Startup%\Xarch.exe
- Xarch = %User Startup%\Xarch.exe
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- discord = %AppDataLocal%\discord.exe
- discord = %AppDataLocal%\discord.exe
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- teleratserver = %User Startup%\teleratserver.exe
- teleratserver = %User Startup%\teleratserver.exe
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- BXIuSsB = %User Startup%\BXIuSsB.exe
- BXIuSsB = %User Startup%\BXIuSsB.exe
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- BXIuSsB.exe = %User Temp%\Adobe\BXIuSsB.exe
- BXIuSsB.exe = %User Temp%\Adobe\BXIuSsB.exe
- In HKEY_CURRENT_USER\Control Panel\Desktop
- Wallpaper = %User Profile%\Pictures\image[Random 30 characters].jpg
- Wallpaper = %User Profile%\Pictures\image[Random 30 characters].jpg
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System
- DisableTaskMgr = 1
- DisableTaskMgr = 1
Step 5
搜索和删除这些文件
- %User Startup%\1.exe
- %User Startup%\archive.exe
- %User Startup%\Xarch.exe
- %User Startup%\teleratserver.exe
- %AppDataLocal%\discord.exe
- %Application Data%\ID
- %Application Data%\fondo_antiguo.jpg
- %User Profile%\Pictures\image[Random 30 characters].jpg
- %User Startup%\BXIuSsB.exe
- %User Temp%\Adobe\BXIuSsB.exe
- %User Temp%\[Random 7 characters]_dat.log
- %Application Data%\delback.bat
- %User Startup%\update.bat
- %User Startup%\1.exe
- %User Startup%\archive.exe
- %User Startup%\Xarch.exe
- %User Startup%\teleratserver.exe
- %AppDataLocal%\discord.exe
- %Application Data%\ID
- %Application Data%\fondo_antiguo.jpg
- %User Profile%\Pictures\image[Random 30 characters].jpg
- %User Startup%\BXIuSsB.exe
- %User Temp%\Adobe\BXIuSsB.exe
- %User Temp%\[Random 7 characters]_dat.log
- %Application Data%\delback.bat
- %User Startup%\update.bat
Step 6
搜索和删除这一文件夹
- %User Temp%\Adobe
Step 7
从备份中恢复加密文件。
Step 8
使用亚信安全产品扫描计算机,并删除检测到的Ransom.MSIL.EGOGEN.THEBBBC文件 如果检测到的文件已被亚信安全产品清除、删除或隔离,则无需采取进一步措施。可以选择直接删除隔离的文件。请参阅知识库页面了解详细信息。
Step 9
重置桌面壁纸




