Ransom.Win32.AGENDA.YPEFR
Ransom:Win32/Qilinloader.AL!MTB (MICROSOFT)
Windows


恶意软件类型:
Ransomware
有破坏性?:
没有
加密?:
没有
In the Wild:
是的
概要
它以文件的形式出现在系统中,可能是其他恶意软件投放的,或者是用户在访问恶意网站时无意中下载的。
技术详细信息
新病毒详细信息
它以文件的形式出现在系统中,可能是其他恶意软件投放的,或者是用户在访问恶意网站时无意中下载的。
安装
它植入下列文件:
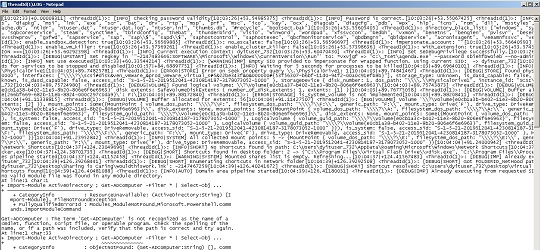
- %Temp%\QLOG\ThreadId(Number).LOG → logs execution status
它添加下列进程:
- "cmd" /C fsutil behavior set SymlinkEvaluation R2R:1
- "cmd" /C fsutil behavior set SymlinkEvaluation R2L:1
- "cmd" /C net use
- "cmd" /C wmic service where name='vss' call ChangeStartMode Manual
- "cmd" /C net start vss
- "cmd" /C vssadmin.exe delete shadows /all /quiet
- "cmd" /C net stop vss
- "cmd" /C wmic service where name='vss' call ChangeStartMode Disabled
- "powershell" $logs = Get-WinEvent -ListLog * | Where-Object {$_.RecordCount} | Select-Object -ExpandProperty LogName ; ForEach ( $l in $logs | Sort | Get-Unique ) {[System.Diagnostics.Eventing.Reader.EventLogSession]::GlobalSession.ClearLog($l)}
- "powershell" -Command "Import-Module ActiveDirectory ; Get-ADComputer -Filter * | Select-Object -ExpandProperty DNSHostName"
- "powershell" -Command "ServerManagerCmd.exe -i RSAT-AD-PowerShell ; Install-WindowsFeature RSAT-AD-PowerShell ; Add-WindowsCapability -Online -Name 'RSAT.ActiveDirectory.DS-LDS.Tools~~~~0.0.1.0'"
它创建下列文件夹:
- %Temp%\QLOG
(注意: %Temp% 是 Windows 的临时文件夹,通常位于 C:\WINDOWS\Temp 或 C:\WINNT\Temp。)
自启动技术
它添加下列注册表项,在系统每次启动时自行执行:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
*vxvjgf = "{Malware file path}" --password {String} --no-admin
其他系统修改
它修改下列注册表项:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
EnableLinkedConnections = 1
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\LanmanServer\Parameters
MaxMpxCt = 65535
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Control\FileSystem
SymlinkRemoteToRemoteEvaluation = 1
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Control\FileSystem
SymlinkRemoteToLocalEvaluation = 1
进程终止
它终止在受感染的系统上运行的下列服务:
- vmms
- mepocs
- memtas
- veeam
- backup
- vss
- sql
- msexchange
- sophos
- msexchange
- msexchange\$
- wsbexchange
- pdvfsservice
- backupexecvssprovider
- backupexecagentaccelerator
- backupexecagentbrowser
- backupexecdivecimediaservice
- backupexecjobengine
- backupexecmanagementservice
- backupexecrpcservice
- gxblr
- gxvss
- gxclmrs
- gxcvd
- gxcimgr
- gxmmm
- gxvsshwprov
- gxfwd
- sapservice
- sap
- sap\$
- sapd\$
- saphostcontrol
- saphostexec
- qbcfmonitorservice
- qbdbmgrn
- qbidpservice
- acronisagent
- veeamnfssvc
- veeamdeploymentservice
- veeamtransportsvc
- mvarmor
- mvarmor64
- vsnapvss
- acrsch2svc
- (.*?)sql(.*?)
它终止在受感染的系统内存中运行的下列进程:
- vmms
- vmwp
- vmcompute
- agntsvc
- dbeng50
- dbsnmp
- encsvc
- excel
- firefox
- infopath
- isqlplussvc
- sql
- msaccess
- mspub
- mydesktopqos
- mydesktopservice
- notepad
- ocautoupds
- ocomm
- ocssd
- onenote
- oracle
- outlook
- powerpnt
- sqbcoreservice
- steam
- synctime
- tbirdconfig
- thebat
- thunderbird
- visio
- winword
- wordpad
- xfssvccon
- bedbh
- vxmon
- benetns
- bengien
- pvlsvr
- beserver
- raw_agent_svc
- vsnapvss
- cagservice
- qbidpservice
- qbdbmgrn
- qbcfmonitorservice
- sap
- teamviewer_service
- teamviewer
- tv_w32
- tv_x64
- cvmountd
- cvd
- cvfwd
- cvods
- saphostexec
- saposcol
- sapstartsrv
- avagent
- avscc
- dellsystemdetect
- enterpriseclient
- veeamnfssvc
- veeamtransportsvc
- veeamdeploymentsvc
- mvdesktopservice
其他详细信息
该程序执行以下操作:
- It terminates itself if it detects that the sample is being executed within a virtual environment.
- It requires the correct input password to proceed in its intended routine.
- Impersonates the privileges of the following process:
- wininit.exe
- winlogon.exe
- lsass.exe
解决方案
Step 2
对于Windows ME和XP用户,在扫描前,请确认已禁用系统还原功能,才可全面扫描计算机。
Step 3
注意:在此恶意软件/间谍软件/灰色软件执行期间,并非所有文件、文件夹和注册表键值和项都会安装到您的计算机上。这可能是由于不完整的安装或其他操作系统条件所致。如果您没有找到相同的文件/文件夹/注册表信息,请继续进行下一步操作。
Step 4
删除该注册表值
注意事项:错误编辑Windows注册表会导致不可挽回的系统故障。只有在您掌握后或在系统管理员的帮助下才能完成这步。或者,请先阅读Microsoft文章,然后再修改计算机注册表。
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- *vxvjgf = {Malware file path} --password {String} --no-admin
- *vxvjgf = {Malware file path} --password {String} --no-admin
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- EnableLinkedConnections = 1
- EnableLinkedConnections = 1
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\LanmanServer\Parameters
- MaxMpxCt = 65535
- MaxMpxCt = 65535
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\FileSystem
- SymlinkRemoteToRemoteEvaluation = 1
- SymlinkRemoteToRemoteEvaluation = 1
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\FileSystem
- SymlinkRemoteToLocalEvaluation = 1
- SymlinkRemoteToLocalEvaluation = 1
Step 5
搜索和删除这些文件夹
- %User Temp%\QLOG
Step 6
搜索和删除该文件
- %Temp%\QLOG\ThreadId(Number).LOG
- {All Available Directories}\README-RECOVER-CcXB9wE4s7.txt
Step 7
使用亚信安全产品扫描计算机,并删除检测到的Ransom.Win32.AGENDA.YPEFR文件 如果检测到的文件已被亚信安全产品清除、删除或隔离,则无需采取进一步措施。可以选择直接删除隔离的文件。请参阅知识库页面了解详细信息。
Step 8
从备份中恢复加密文件。


