Ransom.Win32.ASTROLOCKER.A
BScope.TrojanRansom.Encoder (VBA32)
Windows


恶意软件类型:
Ransomware
有破坏性?:
没有
加密?:
是的
In the Wild:
是的
概要
它以其他恶意软件释放的文件或用户访问恶意网站时不知不觉下载的文件的形式到达系统。
它开始执行然后再删除。
技术详细信息
???????
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
??
???????:
- %User Temp%\{random 8 characters}.bat
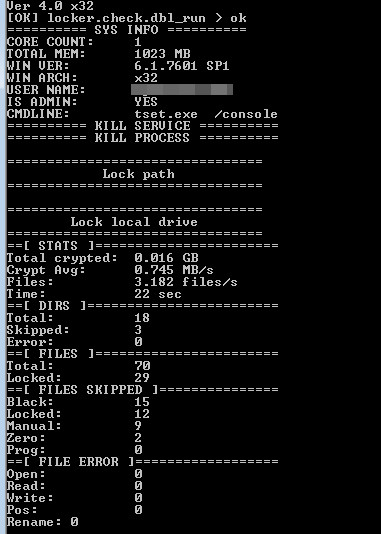
- {Malware Path\Malware File Name and Extension}.log - log file where core count, total memory, OS Information, username, commandline, encrypted files, and malware sample's performance statistics are listed
(??: %User Temp% ?????? Temp ???????? C:\Documents and Settings\{user name}\Local Settings\Temp (Windows 2000(32-bit)?XP ? Server 2003(32-bit))?C:\Users\{user name}\AppData\Local\Temp (Windows Vista?7?8?8.1?2008(64-bit)?2012(64-bit) ? 10(64-bit)?)
???????????
?????????,????????????:
- {32 Hex Characters generated from Volume Serial ID}
??????
???????????????????:
HKEY_CURRENT_USER\Software\Classes\
.{Generated ID}\shell\Open
(Default) = explorer.exe RecoveryManual.html
????
??????????????????:
- database
- msexchange
????????????????????:
- msftesql.exe
- sqlagent.exe
- sqlbrowser.exe
- sqlwriter.exe
- oracle.exe
- ocssd.exe
- dbsnmp.exe
- synctime.exe
- agntsvc.exe
- isqlplussvc.exe
- xfssvccon.exe
- sqlservr.exe
- mydesktopservice.exe
- ocautoupds.exe
- encsvc.exe
- firefoxconfig.exe
- tbirdconfig.exe
- mydesktopqos.exe
- ocomm.exe
- mysqld.exe
- mysqld-nt.exe
- mysqld-opt.exe
- dbeng50.exe
- sqbcoreservice.exe
- excel.exe
- infopath.exe
- msaccess.exe
- mspub.exe
- onenote.exe
- outlook.exe
- powerpnt.exe
- thebat.exe
- steam.exe
- thebat64.exe
- thunderbird.exe
- visio.exe
- winword.exe
- wordpad.exe
- QBW32.exe
- QBW64.exe
- ipython.exe
- wpython.exe
- python.exe
- dumpcap.exe
- procmon.exe
- procmon64.exe
- procexp.exe
- procexp64.exe
????
???????:
- /console - displays the following console window
- /nolog - disable the creation of the log file in the malware directory
- /scan: - specifies what drive type to encrypt
- /marker:{filename} - drops file in infected drive that serves as an infection marker
- /fullpd - encrypts %ProgramData%
- /nodel - disables self deletion after execution
- /nokill - disable process termination
- /fast:{value} - specifies which bytes to encrypt for faster file encryption
- /onlypath /path:{path} - only encrypts a specific path
解决方案
Step 1
对于Windows ME和XP用户,在扫描前,请确认已禁用系统还原功能,才可全面扫描计算机。
Step 2
请注意,在执行此恶意软件/间谍软件/灰色软件期间,并非所有文件、文件夹、注册表项和条目都安装在您的计算机上。这可能是由于安装不完整或其他操作系统条件造成的。如果找不到相同的文件/文件夹/注册表信息,请继续下一步。
Step 3
确定和终止Ransom.Win32.ASTROLOCKER.A检测到的文件
Step 4
删除该注册表值
注意事项:错误编辑Windows注册表会导致不可挽回的系统故障。只有在您掌握后或在系统管理员的帮助下才能完成这步。或者,请先阅读Microsoft文章,然后再修改计算机注册表。
- In HKEY_CURRENT_USER\Software\Classes\.{Generated ID}\shell\Open
- (Default) = explorer.exe RecoveryManual.html
- (Default) = explorer.exe RecoveryManual.html
Step 5
搜索和删除该文件
Step 6
使用亚信安全产品扫描计算机,并删除检测到的Ransom.Win32.ASTROLOCKER.A文件 如果检测到的文件已被亚信安全产品清除、删除或隔离,则无需采取进一步措施。可以选择直接删除隔离的文件。请参阅知识库页面了解详细信息。
Step 7
从备份中还原被加密的文件。


