Ransom.Win32.RHYSIDA.YXDGTT
VHO:Trojan-Ransom.Win32.Agent.gen (KASPERSKY)
Windows


恶意软件类型:
Ransomware
有破坏性?:
没有
加密?:
没有
In the Wild:
是的
概要
N它以其他恶意软件释放的文件或用户访问恶意网站时不知不觉下载的文件的形式到达系统。
它在受感染计算机上收集特定信息。
技术详细信息
新病毒详细信息
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
安装
它添加下列进程:
- %System%\cmd.exe /c cmd.exe /c vssadmin.exe Delete Shadows /All /Quiet
- %System%\cmd.exe /c cmd.exe /c for /F "tokens=*" %1 in ('wevtutil.exe el') DO wevtutil.exe cl "%1"
- %System%\cmd.exe /c cmd.exe /c start powershell.exe -WindowStyle Hidden -Command "Sleep -Milliseconds 1000; schtasks /end /tn Rhsd; schtasks /delete /tn Rhsd /f; schtasks /create /sc ONSTART /tn Rhsd /tr \"'{Malware File Path}\{Malware File Name}.exe' {accepted arguments}\" /ru system; schtasks /run /tn Rhsd /i
- %System%\cmd.exe /c cmd.exe /c start powershell.exe -WindowStyle Hidden -Command \"Sleep -Milliseconds 1000; schtasks /delete /tn Rhsd /f
- %System%\cmd.exe /c cmd.exe /c start ping 127.0.0.1 -n 2 > nul && del /f /q "{Malware File Path}\{Malware File Name}.exe"
- %System%\cmd.exe /c cmd.exe /c reg delete \"HKCU\Contol Panel\Desktop\" /v Wallpaper /f
- %System%\cmd.exe /c cmd.exe /c reg delete \"HKCU\Conttol Panel\Desktop\" /v WallpaperStyle /f
- %System%\cmd.exe /c cmd.exe /c reg add \"HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop\" /v NoChangingWallPaper /t REG_SZ /d 1 /f
- %System%\cmd.exe /c cmd.exe /c reg add \"HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop\" /v NoChangingWallPaper /t REG_SZ /d 1 /f
- %System%\cmd.exe /c cmd.exe /c reg add \"HKCU\Control Panel\Desktop\" /v Wallpaper /t REG_SZ /d \"%Public%\bg.jpg\" /f
- %System%\cmd.exe /c cmd.exe /c reg add \"HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System\" /v Wallpaper /t REG_SZ /d \"%Public%\bg.jpg\" /f
- %System%\cmd.exe /c cmd.exe /c reg add \"HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System\" /v WallpaperStyle /t REG_SZ /d 2 /f
- %System%\cmd.exe /c cmd.exe /c reg add \"HKCU\Control Panel\Desktop\" /v WallpaperStyle /t REG_SZ /d 2 /f
- %System%\cmd.exe /c rundll32.exe user32.dll,UpdatePerUserSystemParameters
(注意: %System% 是 Windows 的 system 文件夹,通常位于 C:\Windows\System (Windows 98 和 ME)、C:\WINNT\System32 (Windows NT 和 2000) 和 C:\WINDOWS\system32 (Windows 2000(32-bit)、XP、Server 2003(32-bit)、Vista、7、8、8.1、2008(64-bit),2012(64bit) 和 10(64-bit))。)
其他系统修改
它通过修改下列注册表项,更改桌面壁纸:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
ActiveDesktop
NoChangingWallPaper = 1
(Note: The default value data of the said registry entry is 0.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
ActiveDesktop
NoChangingWallPaper = 1
(Note: The default value data of the said registry entry is 0.)
HKEY_CURRENT_USER\Control Panel\Desktop
Wallpaper = %Public%\bg.jpg
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
Wallpaper = %Public%\bg.jpg
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
WallpaperStyle = 2
(Note: The default value data of the said registry entry is 0.)
HKEY_CURRENT_USER\Control Panel\Desktop
WallpaperStyle = 2
(Note: The default value data of the said registry entry is 0.)
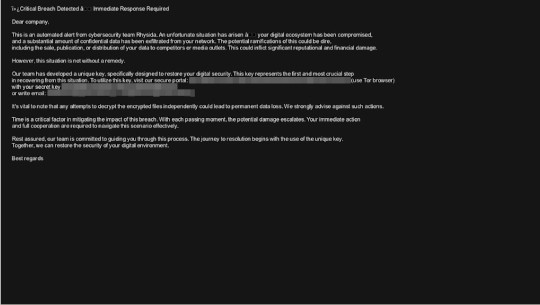
它将系统的桌面壁纸设置为下列图像:
- %Public%\bg.jpg
信息窃取
它在受感染计算机上收集以下信息:
- Number of processors
- System information
它接受下列参数:
- -d {path to encrypt} → used to specify directory to encrypt
- -sr → used to remove/delete itself if -S is not passed as an argument
- -nobg → avoids replacing desktop wallpaper and avoids disabling the ability to replace desktop wallpaper
- -md5
- -S → avoids ransomware routine and creates scheduled task named Rhsd to execute itself on system startup
其他详细信息
它添加下列注册表键值:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies
ActiveDesktop =
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies
ActiveDesktop =
该程序执行以下操作:
- It changes the desktop wallpaper after encryption and prevents the user from changing it back by modifying the NoChangingWallpaper registry value.
- It uses wevtutil.exe to clear Windows event logs.
- It initializes resources based on the number of processors available in the system.
- It encrypts all available drives from A to Z.
解决方案
Step 2
请注意,在执行此恶意软件/间谍软件/灰色软件期间,并非所有文件、文件夹、注册表项和条目都安装在您的计算机上。这可能是由于安装不完整或其他操作系统条件造成的。如果找不到相同的文件/文件夹/注册表信息,请继续下一步。
Step 3
对于Windows ME和XP用户,在扫描前,请确认已禁用系统还原功能,才可全面扫描计算机。
Step 4
重启进入安全模式
Step 6
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this only if you know how to or you can seek your system administrator’s help. You may also check out this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop
- NoChangingWallPaper = 1
- NoChangingWallPaper = 1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop
- NoChangingWallPaper = 1
- NoChangingWallPaper = 1
- In HKEY_CURRENT_USER\Control Panel\Desktop
- Wallpaper = %Public%\bg.jpg
- Wallpaper = %Public%\bg.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- Wallpaper = %Public%\bg.jpg
- Wallpaper = %Public%\bg.jpg
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- WallpaperStyle = 2
- WallpaperStyle = 2
- In HKEY_CURRENT_USER\Control Panel\Desktop
- WallpaperStyle = 2
- WallpaperStyle = 2
Step 7
删除该注册表键值
注意事项:错误编辑Windows注册表会导致不可挽回的系统故障。只有在您掌握后或在系统管理员的帮助下才能完成这步。或者,请先阅读Microsoft文章,然后再修改计算机注册表。
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies
- ActiveDesktop
- ActiveDesktop
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies
- ActiveDesktop
- ActiveDesktop
Step 8
搜索和删除该文件
- %Public%\bg.jpg
Step 9
重启进入正常模式,使用亚信安全产品扫描计算机,检测Ransom.Win32.RHYSIDA.YXDGTT文件 如果检测到的文件已被亚信安全产品清除、删除或隔离,则无需采取进一步措施。可以选择直接删除隔离的文件。请参阅知识库页面了解详细信息。
Step 10
从备份中还原被加密的文件。
Step 11
重置桌面壁纸


